Suppose you are working as an animator for a children's movie. You are responsible for drawing the
main character: an animated dog. Which file format is best suited to your line of work?
GIF
JPEG
PNG
RAW
ANSWER IS GIF
Answers
Answer:
the next slides answers are B & D
Explanation:
Answer:
GIF
Explanation:
Related Questions
A power supply is an electrical transformer that regulates the electricity used by the computer. Select one: A. False B. True
Answers
Answer:
The Answer is B
Explanation:
The power supply converts AC current to DC current and protects the P.C. hardware from being fried from electrical surges. So it regulates electricity.
d What sales methods do you think would work best for selling this product? TIP: Would you sell the product online, over the phone, in a store, etc.? (1-5 sentences. 2.0 points)
e. Describe the methods you would use to pay and motivate sales people to sell this product. Would you use sales quotas or a particular type of commission structure? Why or why not? (1-5 sentences. 2.0 points)
f. What price do you think the company should charge for this product? Explain what factors you considered in deciding what price to charge. (1-6 sentences. 4.0 points)
Answers
Assuming that the chosen product is a smartphone, the sales method that would work to improve to sell this product would be the exposure in a specialized store where the potential customer could try out the device's features and obtain personalized service to solve their doubts.
Sales methodsThese are techniques used for the company to achieve the best performance in its sales, it must be aligned with organizational values and objectives to be effective. Some examples are:
Sales commandConsultative sellingCustomer-centric sellingThe methods used by the cell phone company management to pay and motivate sales personnel to sell this product would be to establish a commission structure focused on specific sales targets.
This strategy would motivate employees to sell more devices focused on increasing their benefits, increasing their productivity and service quality to better serve customers.
The price that the company should charge for the product must be compatible with the market, being the factors for determining the final price, the design, the physical components, the benefits and the value of the brand for the consumers.
Find out more information about sales methods here:
https://brainly.com/question/18957404
An all-in-one printer is also known as a multi-function printer. It includes a printer, scanner, copy machine and / or fax machine.true or false?
Answers
An all-in-one printer is also known as a multi-function printer. It includes a printer, scanner, copy machine and / or fax machine: true.
What is a printer?In Computer technology, a printer can be defined as an electronic output (peripheral) device that is designed and developed for printing paper documents containing texts or images.
What is an all-in-one printer?An all-in-one printer is sometimes referred to as multifunction peripheral or multi-function printer and it can be defined as a type of printer that is designed and developed to comprise all or some of the following;
PrinterScannerCopy machineFax machine.Read more on printer here: brainly.com/question/17100575
#SPJ1
nowadays, which is more effective and efficient to use, the manual database or manual database? explain
Answers
Answer:
Advantages of Electronic Databases over Manual databases
Electronic databases make it easier to query, search, filter and retrieve required data. Electronic databases allow centralised use of information amongst many users over a network and therefore reduce duplication, e.g in banks.
Which cloud computing deployment model requires the use of a unifying technology platform to tie together components from different providers?
Answers
Hybrid cloud is computing deployment model requires the use of a unifying technology platform to tie together components from different providers.
What is hybrid cloud?Hybrid cloud is defined as one in which all applications are use to running in a combination of other or different environment.
There are many risk of hybrid cloud and they are insecure cloud data transmission, risk of supply chain, compliance falling out and several other risks are also present with hybrid cloud.
The main advantage of hybrid cloud is that it provides security,cost, speed, and control.
Therefore ,Hybrid cloud is computing deployment model requires the use of a unifying technology platform to tie together components from different providers.
Learn more about hybrid cloud here:
https://brainly.com/question/27108963
#SPJ4
a information flow relates to the information that is produced by a company and sent along to another organization
Answers
That's correct! Information flow refers to the movement of information within and between organizations.
In a business context, this could include communication between different departments or teams within the same company, as well as communication with external partners, suppliers, or customers. Effective information flow is essential for ensuring that all relevant parties have access to the information they need to make informed decisions and carry out their work effectively.
In addition to internal information flow, organizations also engage in information exchange with external entities, such as suppliers, customers, partners, or regulatory bodies. This external information flow involves sharing information related to orders, sales, market trends, industry standards, compliance, and other relevant aspects.
It's important for organizations to establish effective communication channels, information systems, and protocols to facilitate smooth information flow, ensure accuracy and reliability of information, and enhance overall organizational efficiency and effectiveness.
So, while information flow is crucial for organizations, it primarily refers to the movement of information within the organization rather than specifically between organizations.
Learn more about Information flow refers to the movement from
https://brainly.com/question/29734722
#SPJ11
PLEASE HELP WITH MY COMPUTER
this thing is popped up and it's annoying. I'm on a HP laptop how do i get rid of it?

Answers
Answer:
Escape or turn it off then back on??
Explanation:
I'm not very sure what is going on but idfk
Under which accounting method are most income statement accounts translated at the average exchange rate for the period ?
A) current/concurrent method
B) monetary/nonmonetary methode
C)temporal method
D)All of the options
Answers
Under the accounting method where most income statement accounts are translated at the average exchange rate for the period, the correct option is D) All of the options.
The current/concurrent method considers both monetary and nonmonetary balance sheet items and translates income statement accounts at the average exchange rate for the period. This method takes into account the fluctuations in exchange rates throughout the period and provides a more accurate representation of the financial results in the reporting currency.
By using the average exchange rate, the impact of exchange rate fluctuations on income statement accounts is spread out over the period, reducing the impact of currency volatility on reported earnings.
Learn more about accounting method here: brainly.com/question/30512760
#SPJ11
in a block in a blockchain what represents the transactional data, sender, receiver, and number of coins? group of answer choices data hash previous hash proof-of-stake
Answers
In a block in a blockchain, a resource which represent the transactional data, sender, receiver, and number of coins is: A. data.
What is a blockchain?A blockchain can be defined as a digital and dynamic financial system that is designed and developed to be used in recording and maintaining transactions that are associated with or made through the use of a bitcoin, usually as a database containing various set of data.
In this context, we can infer and logically deduce that data is a resource that typically represent all of the transactional data, sender, recipient (receiver), and the number of bitcoins in a block in a blockchain.
Read more on blockchain here: brainly.com/question/25700270
#SPJ1
What sort of negative outcomes are possible for this type of risk?
Answers
Answer:
not enough to go on
Explanation:
What is more important, the individual or the collective (the group)? Why?
Least 2 paragraphs
Answers
Answer:
It's complicated.
Explanation:
I don't want to write the entire thing for you. However, there are multiple ways to think about this. Individualism vs. collectivism (groupthink) is a big debate itself.
---
Couple of points for the individual:
- Choice of personal freedom
- Not overly complicated (focuses on the self)
- The needs of the self comes before the needs of the many (in some situations, this might prove helpful)
Couple of points for the group:
- Shared thoughts and feelings may result in a bigger camaraderie than the thoughts of the self
- Compassion for humanity vs. selfishness
- A tendency to forge alliances
---
Interpret these for yourself. One's own mind is crucial in understanding the philosophical structures of life's biggest questions. And for it only being 2 paragraphs. Like, isn't that 10 sentences? I don't know what your teacher is looking for but your own personal thoughts on the matter may be good writing.
---
Here's a very-hard-to-see-the-text-but-helpful website, from the City University of New York (this talks about the theories of the individual and group interest in relation to government, but it may provide useful to you in understanding): https://www.qcc.cuny.edu/socialsciences/ppecorino/intro_text/Chapter%2010%20Political%20Philosophy/Group_vs_Individual_Interest.htm
__________ variables are factors that come from outside a theoretical system and cannot be explained by that system.
Answers
Exogenous variables are factors that come from outside a theoretical system and cannot be explained by that system.
Given data:
The variables referred to in the statement are called "exogenous" variables. Exogenous variables are factors or influences that originate from outside the system being studied or analyzed. These variables cannot be explained or determined by the internal workings of the system itself.
Exogenous variables are important in various fields such as economics, social sciences, and systems analysis. They are typically used to account for external factors that can affect the behavior or outcomes of a system. These variables are considered independent of the system and are often treated as given or assumed rather than being directly influenced or controlled by the system.
To learn more about endogenous and exogenous variables click:
https://brainly.com/question/32230531
#SPJ4
Logical operators must be used in order to combine two or more conditions in a query. ____________________
Answers
True In this example, there are six conditions that must be satisfied for a record to be retrieved. Each of these conditions is separated by either the AND or the OR logical operator.
Logical operators are used to combine two or more conditions in a query. A condition is a combination of fields and operators that is used to specify the subset of data that is to be retrieved or updated from a table. The condition(s) should be enclosed in parentheses, and each condition should be separated by either the AND or the OR logical operator, as shown below: SELECT * FROM table _name.
Where condition1 AND condition2 AND condition3 OR condition4 AND condition5 OR condition6;This SQL query is used to retrieve all records from the table named "table_ name" that meet the specified conditions. In this example, there are six conditions that must be satisfied for a record to be retrieved. Each of these conditions is separated by either the AND or the OR logical operator.
To know more about logical operator visit:
https://brainly.com/question/14617992
#SPJ11
in a basic program with 3 IF statements, there will always be _________ END IIF's.
a)2
b)3
c)4
Answers
Answer:
c)4
Explanation:
Hope it could helps you
b. What significant values have you learned while learning the tools and utensils?
Answers
What is use of enum in Java?
Answers
Enums in Java are used to create a list of named constants. It is a type-safe way to create a collection of related items and helps to make code more readable and maintainable. It also helps to identify specific constants in the code more easily.
Enums in Java are used to create a list of named constants. They are declared using the enum keyword and can contain fields, methods, and constructors. It is a type-safe way to create a collection of related items and helps to make code more readable and maintainable. Enums can also be used to identify specific constants in the code more easily. Enums can be used in switch statements and for loop statements, as well as when creating collections such as Lists, Maps, and Sets. They can also be used to create a custom data type. Enums also help to prevent bugs caused by typos and can be used to create self-documenting code. Furthermore, they are more efficient than using constants, as the constants are only loaded into memory once. Overall, using enums in Java can help to make code more robust and maintainable.
Learn more about Java here:
brainly.com/question/28452505
#SPJ4
Define computer system?
Answers
Answer:
A computer system is a "complete" computer that includes the hardware, operating system (main software), and peripheral equipment needed and used for "full" operation. This term may also refer to a group of computers that are linked and function together, such as a computer network or computer cluster.
which is NOT something that a game producer needs to do?
A- make sure the team has the tools that they need to be successful
B- create and support ways for the team to collaborate
C- plan the script, characters, and how the game is played
D- choose the programming language that will be used to develop the game
Answers
Answer:
Plan the script, characters, and how the game is played
An action that a game producer needs not to do is to plan the script, characters, and how the game is played. Thus, the correct option for this question is C.
What are the actions that a game producer needs to do?The actions that a game producer needs to do are as follows:
They choose the programming language that will be used to develop the game.They considerably create and support ways for the team to collaborate on the same mission. They always make sure the team has the tools that they need to be successful togetherly.Apart from this, video game producers have to manage a lot of things. Such as constructing video games, playing an executive role during each development phase, ensuring the quality of the project, managing the timeliness of the teams working on the same project (duration), etc.
Therefore, an action that a game producer needs not do is plan the script, characters, and how the game is played. Thus, the correct option for this question is C.
To learn more about Game producers, refer to the link:
https://brainly.com/question/3863314
#SPJ2
Select the correct answer.
What needs to be defined throughout an animation sequence to define the start and end points of motion?
A frames
B. characters
C. key frames
D. movement
Answers
An important part of the development of transport is safety. how can you, when you get around in different ways, contribute to making it safer on the roads
Answers
Answer:
I need help I don't get a this questions please asap?
Explanation: Head-on collisions. Some simple solutions can help to reduce the risk of head-on crashes. ...
Run-off road crashes. This is when a vehicle collides with a stationary object, such as a sign or lamppost, after leaving the road. ...
Intersection crashes. ...
Vulnerable road users. ...
Much work to be done.
Aug 31, 2018
A radio station requires DJs to play 3 commercials for every 15 songs they play.What is the unit rate of songs to commercial?
Answers
Since the radio station requires DJs to play 3 commercials for every 15 songs they play, the unit rate of songs to commercial is known to be 5:1.
What do you mean by advertisements?A commercial is a piece of company advertising. Selling products or services for profit is considered commercial activity. It is one that commercial trading occurs in the forward and futures markets, and also for heading-related reasons.
Note that By reducing the ratio of the two ads to every ten songs, we can figure this out, making 10:2 into 5:1.
That is 15/3 = 5.
Therefore, Since the radio station requires DJs to play 3 commercials for every 15 songs they play, the unit rate of songs to commercial is known to be 5:1.
Learn more about commercials from
https://brainly.com/question/694246
#SPJ1
A number of your clients seem to be abusing the change request process. You have seen an increase in the number of frivolous requests. These, of course, must be researched and resolved, and that takes away from the time that your team members can do actual project work. From a process point of view what might you do? Be specific.
2. What are the advantages and disadvantages of checking upon the accu- racy of status reports filed by your team members?
Answers
To address the abuse of the change request process and the increase in frivolous requests, specific actions can be taken from a process point of view.
To address the abuse of the change request process, several specific steps can be taken. First, stricter guidelines can be established for submitting change requests, including clear criteria for what constitutes a valid request.
Second, a review committee can be formed to assess and evaluate each change request, ensuring that only legitimate and impactful requests proceed.
Third, improving communication and education about the change process can help educate clients on the importance of valid requests and discourage frivolous submissions.
Finally, consequences can be implemented for submitting frivolous requests, such as additional fees or limitations on future requests, to deter abuse.
Checking the accuracy of status reports filed by team members has advantages and disadvantages. On the positive side, it ensures transparency and accountability within the team, as it allows project managers to verify the progress and accuracy of reported information.
It provides an opportunity to identify and address any discrepancies or issues promptly. However, there are also disadvantages to consider. Checking status reports can be time-consuming, especially if the team is large or if reports need to be reviewed frequently.
It may also create a sense of mistrust or micromanagement within the team if not handled carefully. Balancing the need for accuracy with trust and empowerment is crucial to maintain a positive team dynamic.
learn more about guidelines here:
https://brainly.com/question/31575794
#SPJ11
identity the advantages and disadvantages of the types of computers
Answers
There are three sorts of computers based on their data handling capabilities: The analog computer. Computer that is digital. Computer hybrid. There are both benefits and drawbacks of using a laptop computer.
What are the benefits and drawbacks of computers?Nowadays, computers play an important part in human life. One of the most significant advantages of computers is their remarkable speed, which allows humans to complete tasks in a matter of seconds. The cost/stores are enormous - the amount of knowledge it is a coffee cost solution. A person can save a lot of data on a coffee budget. It is extremely speedy and allows us to do our work in record time. Stores Massive Datasets: Computers have the ability to store a significant amount of data. It is capable of storing files, documents, photos, and movies. Accur A disadvantage is defined as an unpleasant condition or something that puts someone in an undesirable situation.To learn more about computers, refer to:
https://brainly.com/question/21474169
#SPJ4
Firewall and IDS a. Where is a firewall typically deployed? b. What are firewalls used for? c. What are the contents that a firewall inspects?
d. Where is an IDS typically deployed?
e. What are the contents tht an IDS inpects?
f. What is purpose of using DMZ?
Answers
a. Firewall deployed at various points within a computer network to protect it from unauthorized access.b. Several purposes to enhance network security.c.Several aspects of network traffic to make decisions.d. Within a computer network to monitor and detect potential security breaches. e. Inspects various aspects of network traffic. f. To provide an additional layer of security for a network by segregating and isolating certain services.
a.
A firewall is typically deployed at various points within a computer network to protect it from unauthorized access and malicious activities. The specific locations where firewalls are commonly deployed include: Network Perimeter and data center.
b.
Firewalls are used for several purposes to enhance network security. Some of the primary uses of firewalls include:
Network Security: Firewalls act as a barrier between a trusted internal network and untrusted external networks, such as the internet. Access Control: Firewalls enforce access control policies by allowing or denying network traffic based on predefined rules.Threat Prevention: Firewalls incorporate various security features to detect and prevent network-based threats, such as malware, viruses, intrusion attempts, and denial-of-service (DoS) attacks.c.
Firewalls inspect several aspects of network traffic to make decisions on whether to allow or block it based on predefined rules. The specific contents that a firewall inspects include:
Source and Destination IP Addresses: Firewalls examine the source and destination IP addresses of network packets to determine if they match specified rules.Port Numbers: Firewalls inspect the port numbers associated with network traffic. Ports are used to identify specific services or applications running on a system.Protocols: Firewalls inspect the protocols used in network communications, such as TCP (Transmission Control Protocol), UDP (User Datagram Protocol), ICMP (Internet Control Message Protocol), and others.Packet Contents: Firewalls can analyze the contents of network packets beyond just header information.Session State: Stateful firewalls maintain information about the state of network connections.d.
An Intrusion Detection System (IDS) is typically deployed within a computer network to monitor and detect potential security breaches or suspicious activities. The specific locations where IDSs are commonly deployed include:
Network Perimeter: IDSs are often deployed at the network perimeter, where they can monitor incoming and outgoing traffic between the internal network and the external internet.Internal Network: IDSs may also be deployed within the internal network to monitor traffic between different segments, such as different departments or zones within an organization.Data Centers: IDSs are commonly deployed within data centers to monitor and protect critical servers, databases, and other infrastructure components. Host-based: In addition to network-based IDS, there are also host-based IDSs (HIDS) that are installed directly on individual hosts or servers.Cloud Environments: With the increasing adoption of cloud computing, IDSs can also be deployed within cloud environments to monitor network traffic and detect potential threats targeting cloud-based applications, virtual machines, or containers.e.
An Intrusion Detection System (IDS) inspects various aspects of network traffic and system activities to identify potential security breaches or suspicious behavior. The specific contents that an IDS inspects include:
Network Traffic: IDSs analyze network packets to detect anomalies or patterns associated with malicious activities.Packet Headers: IDSs examine the headers of network packets to extract information such as source and destination IP addresses, port numbers, protocol types, and flags. Payload Analysis: IDSs may perform deep packet inspection (DPI) to inspect the contents of network packets beyond the headers.f.
The purpose of using a DMZ (Demilitarized Zone) is to provide an additional layer of security for a network by segregating and isolating certain services or systems from both the internal network and the external internet. The key purposes of using a DMZ include:
Security Isolation: By placing systems or services in a DMZ, organizations create a buffer zone that separates their internal network (which contains sensitive or critical resources) from external networks.Public-Facing Services: DMZs are commonly used to host public-facing services that need to be accessible from the internet, such as web servers, email servers, FTP servers, or DNS servers. Access Control: The DMZ allows organizations to implement stricter access controls for incoming and outgoing traffic.To learn more about firewall: https://brainly.com/question/13693641
#SPJ11
help me please help help

Answers
Answer:
C
Explanation:
The concept of superheros
Answer: C.
Explanation:
cause that concept is oooooooooooooooooooooooooooooold
A mail server is like an electronic post office:
Answers
A mail server is like an electronic post office because it functions as a central hub for sending, receiving, and managing electronic messages (emails) between users on the internet. Just as a traditional post office sorts and distributes physical mail, a mail server processes and routes electronic mail to the intended recipients.
1. A mail server is a type of computer program that is designed to handle email messages. It works like an electronic post office in many ways, providing a way for users to send and receive messages across the internet.
2. Just like a post office, a mail server has several important functions. First and foremost, it is responsible for receiving incoming messages and storing them until they can be delivered to the intended recipient. When a user sends an email, the mail server processes the message and sends it on to the recipient's email server. The mail server may also perform spam filtering and virus scanning to protect the recipient from malicious content.
3. In addition to handling incoming messages, a mail server also has the ability to send outgoing messages. This is useful for sending newsletters, notifications, and other types of messages to a large number of recipients at once.
To learn more about mail server : https://brainly.com/question/15710969
#SPJ11
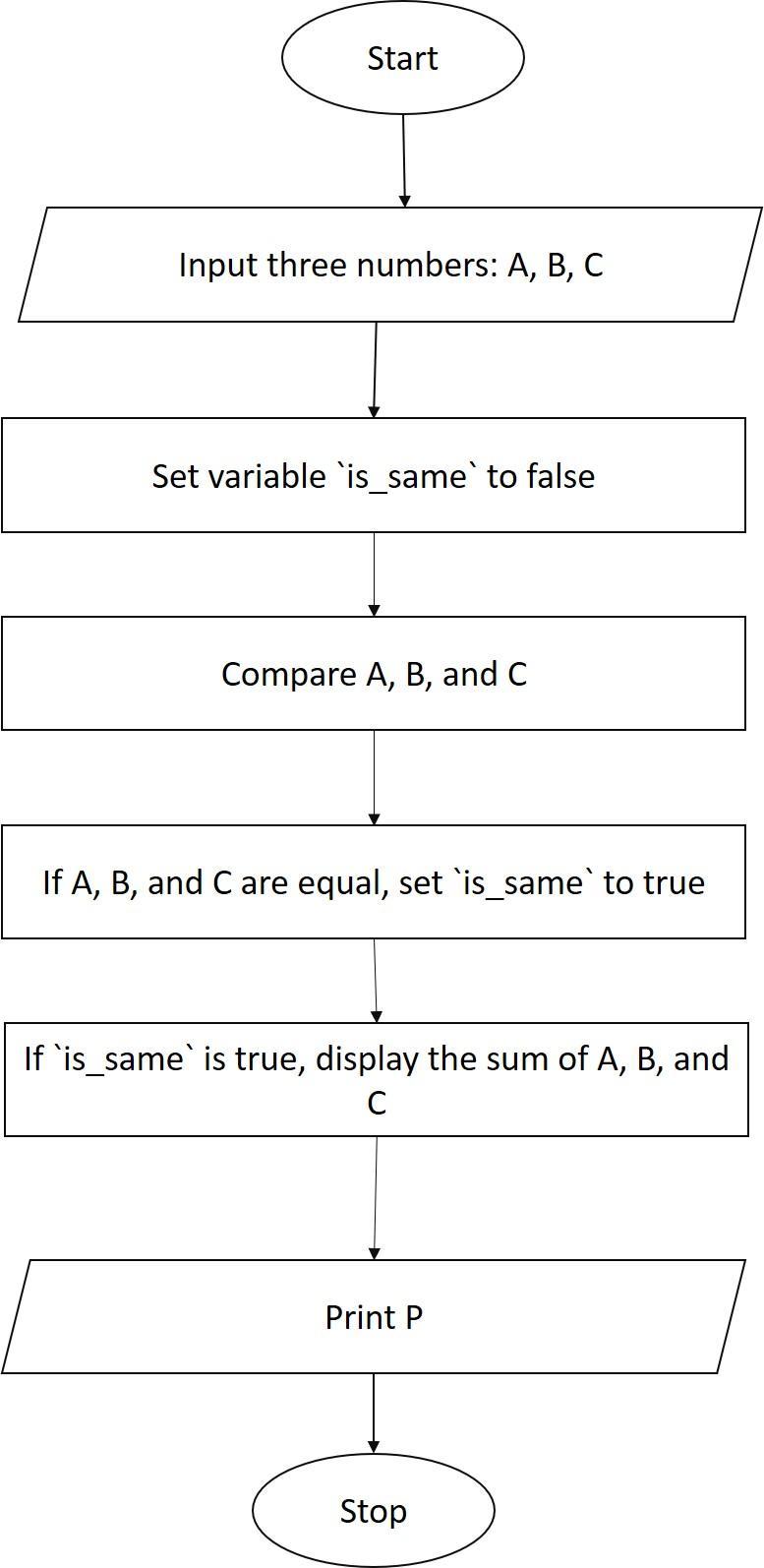
Draw the flowchart to accept three numbers check if they are same then display sum otherwise display product
Answers
The required flow chart is depcied as follows
Start
Input three numbers, A,B, and C
Compare A, B, and C
If A, B, and C are the same, then
Display the sum of A, B, and C
Else
Display the product of A, B, and C
End
What is the explanation for the above?The program starts by inputting three numbers, A, B, and C.
The program then compares A, B, and C.
If A, B, and C are the same, then the program displays the sum of A, B, and C.
Otherwise, the program displays the product of A, B, and C.
The program ends.
Learn more about Flow Chart at:
https://brainly.com/question/6532130
#SPJ1
When one-year-old Terrace is in new surroundings, he will explore freely if his mother watches him. If she leaves the room he begins to cry, but when she returns he smiles and stops fussing. Terrace would be considered a(n) ____ infant.
Answers
Terrace would be considered a secure infant. Terrace's behavior indicates a secure attachment style. When his mother is present, he feels safe and explores freely, displaying trust in her presence.
However, when his mother leaves the room, he experiences distress and cries, showing a fear of abandonment or separation anxiety. When she returns, he smiles and stops fussing, indicating that her presence reassures and comforts him. This pattern of behavior suggests that Terrace has developed a secure attachment to his mother, characterized by a healthy bond and trust in their relationship. He seeks proximity to his mother for emotional support and uses her as a secure base to explore the environment.
Learn more about secure infant here:
https://brainly.com/question/32340946
#SPJ11
select the name, creaturetype, creaturesubtype, gender, and appearance from litcharacters for creatures who have made 5 or more appearances (this includes characters that have made 5 appearances). order ascending by the character id. what is the first entry?
Answers
I'm sorry, but as an I don't have access to a specific database or its data. Therefore, I cannot retrieve the first entry from the "litcharacters" table as requested.
To obtain the first entry from the "litcharacters" table with the given conditions, you would need to execute a SQL query on the database that contains the table. The query would look something like this:
SELECT name, creaturetype, creaturesubtype, gender, appearance
FROM litcharacters
WHERE appearance >= 5
ORDER BY character_id ASC
LIMIT 1;
Executing this query on the appropriate database would give you the first entry from the "litcharacters" table that meets the criteria of having 5 or more appearances.
Learn more about database here
https://brainly.com/question/24027204
#SPJ11
Arrange the steps involved in natural language generation.
picking words and connecting them to
form sentences
setting the tone and style of the sentence
accessing content from some knowledge base
mapping the sentence plan into sentence structure
Answers
Answer:
1. accessing content from some knowledge base.
2. picking words and connecting them to form sentences.
3. setting the tone and style of the sentence.
4. mapping the sentence plan into sentence structure.
Explanation:
Natural language generation can be defined as a part of artificial intelligence (AI) which typically involves developing responses by an AI in order to enable the computer engage in a useful conversation.
This ultimately implies that, the computer has to generate meaningful data (phrases and sentences) from the internal database.
Basically, the steps involved in natural language generation in a chronological order are listed below;
1. Text planning: accessing content from some knowledge base.
2. Picking words and connecting them to form sentences
3. Sentence planning: setting the tone and style of the sentence.
4. Text realization: mapping the sentence plan into sentence structure.