write a function that takes a single input parameter and returns a string containing the front half of the string
Answers
Here's an example of how to implement such a function:
```pythondef front_half(s:str)->str: return s[:len(s)//2]```
To write a function that takes a single input parameter and returns a string containing the front half of the string, you can use the slice operator in Python.
In the above example, we define a function called `front_half` that takes a single input parameter `s` of type string.
We then use the slice operator to extract the front half of the string by taking a slice of the string from the start to the middle position (using integer division to get the floor value of the length of the string divided by 2). We then return this substring as the output of the function.
Learn more about python at:
https://brainly.com/question/19168392
#SPJ11
Related Questions
All variables are----------------------------------------------- help please
Answers
Answer:
variables are any characteristics that can take on different values, such as height, age, species I think
Answer
A variable basically works as a "placeholder" for anything that might change a majority of the time.
Examples
In science one may call a factor in a experiment that is subject to change a variable.
In math the term is used for a symbol that we do not know yet, such as x or y. Typically in math a variable is a letter.
In computer programming, variables are used to store information to be referenced and used by a computer program. They do give a way of naming data with a descriptive name as well so programs can be understood more clearly. When you go to assign values to the "variable" you are basically assigning individual variables such as the ones above in a way.
What action will help make a social media campaign successful? (5 points) Group of answer choices Avoid challenging the audience Create a big goal Avoid using personal stories Show others how to get involved
Answers
You need interesting content if you want to succeed on social media. More clients are drawn to visual content these days than to notes or paragraphs regarding your goods or services.
What social media campaign successful?Creating engaging content with a message that appeals to your target audience is essential to the success of your media strategy. For the social media sites you'll be using, and for your target, your material should be customized.
Therefore, As an illustration, you can see that I also share visual information on social media platforms, and it is really effective.
Learn more about social media here:
https://brainly.com/question/27588046
#SPJ1
what does the first number in a zip code represent?
Answers
so.. the answer is “ The first digit in a ZIP code represents a defined group of U.S. states. “
hope this helps!!
threadless is an online store that sells shirts with user-submitted designs. anyone can register and submit a design, then community members score the designs submitted each week, and threadless picks the top designs to sell in their store each week. designers receive royalties for every shirt sold. here's one example of a submitted user design: a screenshot of a threadless shirt design submission, of a dandelion riding a motorcycle, a username of the designer, and 1-5 scoring buttons. what situation would be least likely to threaten the success of the threadless crowdsourcing model? choose 1 answer: choose 1 answer: (choice a) if a large number of new designers suddenly join the community and submit double the number of designs. a if a large number of new designers suddenly join the community and submit double the number of designs. (choice b) if designers discover a new site with higher royalties for winning designs and only submit their designs on the new site. b if designers discover a new site with higher royalties for winning designs and only submit their designs on the new site. (choice c) if designers submit designs that aren't attractive to the threadless community and public at large. c if designers submit designs that aren't attractive to the threadless community and public at large. (choice d) if community members all decide to vote for shirts that they have no interest in owning. d if community members all decide to vote for shirts that they have no interest in owning.
Answers
Conciseness is also important and irrelevant parts of the question or typos should be ignored.The situation that would be least likely to threaten the success of the Thread less crowdsourcing model is if community members all decide to vote for shirts that they have no interest in owning.option b is correct
Thread less is an online store that sells shirts with user-submitted designs. Anyone can register and submit a design, then community members score the designs submitted each week, and Thread less picks the top designs to sell in their store each week. Designers receive royalties for every shirt sold.One example of a submitted user design is a screenshot of a Thread less shirt design submission, of a dandelion riding a motorcycle, a username of the designer, and 1-5 scoring buttons. The design has to appeal to the Thread less community and the public at large for it to sell.If a large number of new designers suddenly join the community and submit double the number of designs, it may be a good thing for the store. More designs could mean more choices for customers and potentially more sales. If designers discover a new site with higher royalties for winning designs and only submit their designs on the new site, this could be a threat to the Thread less crowdsourcing model. However, this situation is not the least likely to threaten the success of the model, as it involves the designers who submit designs.The situation that would be least likely to threaten the success of the Thread less crowdsourcing model is if community members all decide to vote for shirts that they have no interest in owning. This could lead to the selection of designs that are not attractive to the public and may not sell well. Therefore, it is important for the Thread less community members to be honest and vote for designs that appeal to them and are likely to be successful.For such more question on crowdsourcing
https://brainly.com/question/28360136
#SPJ11
Which of the following is not true of how computers represent complex information
Answers
Answer: c. Depending on context the same sequence of bits may represent different types of information.
Explanation:
The options for the question are:
A. Computing devices use patterns of bits to represent complex information
B. Abstraction helps represent complex information by surfacing complexity that might otherwise be hidden
C. Depending on context the same sequence of bits may represent different types of information
D. Common abstractions that are represented by computing devices include numbers, characters, and color.
The following are true of how computers represent complex information:
• Computing devices use patterns of bits to represent complex information
• helps represent complex information by surfacing complexity that might otherwise be hidden
• Common abstractions that are represented by computing devices include numbers, characters, and color.
Therefore, the option that is not true of how computers represent complex information is that "depending on context the same sequence of bits may represent different types of information".
It is not true that abstraction helps represent complex information by surfacing complexity that might otherwise be hidden.
The term abstraction is used very often in computer science and describes the separation between concept and implementation. Structures are defined by their meaning, while the detailed information about the functionality remains hidden.
Abstraction aims to ignore the details of the implementation and to derive a general scheme for solving the problem. A computer program can thus have different levels of abstraction, with a different level of information content being disclosed to the programmer on each level.
A low level abstraction includes details about the hardware on which the program is running. Higher levels of abstraction, on the other hand, deal with the business logic of the software.
Learn more in https://brainly.com/question/13391804

Filtering out the details to leave the general characteristics is referred to as_____.
A. refinement
B. decomposition
C. pattern recognition
D. abstraction
Answers
Answer:
✔️ A. abstraction
Explanation:
Answer:
abstraction is correct
Explanation:
using fisher and ury's method of principled negotiation, how would you separate the people from the problem
Answers
Using Fisher and Ury's method of principled negotiation, separating the people from the problem involves focusing on the interests of each party rather than their positions.
This means understanding the underlying needs, desires, and concerns of both parties and working towards finding a solution that meets those needs. By depersonalizing the problem and focusing on the issues at hand, it becomes easier to work together towards a mutually beneficial agreement. This approach of principled negotiation also involves active listening, reframing the problem in a way that focuses on common goals, and exploring alternative solutions.
In doing so, the parties can come together to collaborate on a solution that satisfies their respective interests without allowing personal conflicts to interfere.
To know more about Principled Negotiation, click here:
https://brainly.com/question/31329033
#SPJ11
I need help ASAP
(What is done when Python compiles your program?)
It is converted into octal numbers.
It is converted into bytemap.
It is converted into hexadecimal.
It is converted into bytecode.
Answers
Answer:
It is converted into bytecode.
a. Write a program that reads a file "data.in" that can be of any type (exe, pdf, doc, etc), and then copy its content to another file "data.out". For example, if it's a pdf file, "data.out" should be opened successfully by a PDF reader. If it's a video file, the output file can be replayed.
b. Please use binary file read/write for your program.
c. The file size ranges between 1MB-50MB.
d. Comment at the top of the program for how to execute your program
Answers
To write a program that reads a file "data.in" of any type (exe, pdf, doc, etc) and then copies its content to another file "data.out" successfully opened by the respective program, the following code may be written with binary file read/write:```c#include
using namespace std;
int main() {
string fileName = "data.in";
string outFileName = "data.out";
ifstream inputFile(fileName, ios::binary | ios::ate);
int size = inputFile.tellg();
inputFile.seekg(0, ios::beg);
ofstream outputFile(outFileName, ios::binary);
char* buffer = new char[size];
inputFile.read(buffer, size);
outputFile.write(buffer, size);
delete[] buffer;
inputFile.close();
outputFile.close();
return 0;
Executing the program: Run the program as you would any other C++ program in the command prompt by following these steps:
1. Make sure you have a C++ compiler installed on your computer (such as gcc).
2. Save the code to a file with the ".cpp" file extension (such as "filecopy.cpp").
3. Open the command prompt and navigate to the directory where the code file is located.
4. Type "g++ filecopy.cpp -o filecopy" and press enter.
5. Type "filecopy" and press enter.
To learn more about "program", visit: https://brainly.com/question/31137060
#SPJ11
Forests are crucial to the health of our planet because they __________. A. Can easily be cut down to make room for agriculture and cattle grazing B. Provide homes for species of plants that are used to make medicines C. Clean and protect the atmosphere by absorbing carbon dioxide and releasing oxygen D. Provide fuel and lumber for houses and industries
Answers
Answer:
C
Explanation:
Trees release oxygen :)
Answer:
C. clean and protect the atmosphere by absorbing carbon dioxide and releasing oxygen
Explanation:
what transport protocol/ports do dns and dhcp use?
Answers
The uses of transport protocol/ports do dns and dhcp are described.
What is DNS?DNS (Domain Name System) and DHCP (Dynamic Host Configuration Protocol) use different transport protocols and ports.
DNS primarily uses the User Datagram Protocol (UDP) as its transport protocol, although it can also use TCP. DNS uses port 53 for both UDP and TCP traffic. Most DNS traffic uses UDP, but if a DNS response exceeds the maximum length of a UDP packet (512 bytes), it will use TCP instead.
DHCP primarily uses UDP as its transport protocol. DHCP uses port 67 for the DHCP server and port 68 for the DHCP client. When a device requests an IP address via DHCP, it sends a broadcast packet to the local network on port 67.
The DHCP server receives the broadcast packet and responds on port 68 with an offer of an available IP address. The client then sends a request for that IP address, and the server sends an acknowledgement back to the client to confirm the assignment of the IP address.
To know more about Domain visit:
brainly.com/question/30408285
#SPJ4
what is the name of a computer system that is designed to perform a specific and dedicated function?
Answers
Answer:
A program.
Explanation:
A program is designed to perform a single operation. For example, a SpeedGrader program is designed for teachers to quickly grade assignments.
________ can be used to produce automatic responses if data have been altered. ________ can be used to produce automatic responses if data have been altered. SQL code DML triggers Mirroring DDL triggers
Answers
DML triggers can be used to produce automatic responses if data have been altered. SQL code and DDL triggers may also be used, but they are not specifically designed for monitoring and responding to changes in data.
Mirroring is a data replication technology that involves copying data from one server to another without the use of triggers. It ensures data redundancy by maintaining an identical copy of the data on multiple servers, providing a failover mechanism in case of server failure. Mirroring is commonly used for high availability and disaster recovery purposes in database systems.
To know more about DML triggers visit:
brainly.com/question/31200286
#SPJ11
Use the drop-down menus to select the answer that best completes each statement.
A person who finds a way to watch a recent movie online without paying for it is violating
A student who posts an inappropriate comment about a person via social media is violating
A student who visits a school-banned website that contains offensive content is violating school rules on
Answers
A person who finds a way to watch a recent movie online without paying for it is violating movie copyright.
A student who posts an inappropriate comment about a person via social media is violating their rights to privacy.
A student who visits a school-banned website that contains offensive content is violating school rules on censorship.
What is Movie Piracy?This refers to the illegal copying and selling of DVDs and CDs without the permission of the owner.
Hence, we can see that a person who finds a way to watch a recent movie online without paying for it is violating movie copyright.
A student who posts an inappropriate comment about a person via social media is violating their rights to privacy.
A student who visits a school-banned website that contains offensive content is violating school rules on censorship.
Read more about movie piracy here:
https://brainly.com/question/8042416
#SPJ1
Answer: all the answers are here
Explanation:

Mathias has very supportive parents who will let him play video games but only after he has finished all of his homework. What type of parenting style does this best represent?.
Answers
Authoritative parenting style. type of parenting style does this best representatives
What are representatives?The term representative refers that the person who is serving to represent something as we see there are some diplomats are being there who represent the country, and there is someone who represents the states as there are different peoples who are being there in it. As there are different players as we see, they represent the nation as well.
As Mathias's parents are having an authoritative parenting style by which they care for their children as well they know about the children future as well that why they are doing their best for there children they are doing their authoritative parenting style which they can secure their child's future as well
Therefore, The Type of parenting style this best representative
Learn more about representatives here:
https://brainly.com/question/13246446
#SPJ1
What icon indicated video mode?
Av
Tv
The video camera icon
Answers
The video camera icon indicated video mode.
The video camera icon is a universally recognized symbol that indicates video mode on electronic devices such as cameras, smartphones, and video recorders. This icon usually appears on the interface of the device, usually on the screen or as a button that you can press, when you are in video mode, and it allows you to record videos.
AV and TV icons are related to audio-video and television, but they are not used specifically to indicate video mode. AV icon can be used for different purposes such as indicating the audio-video input/output of a device or indicating an audio-video format. The TV icon is used to indicate the television mode, which typically refers to the display mode of a device.
Select the software which is used to convert audio data to text .
Answers
Answer:
The process of converting an audio file into a text file is audio transcription. That can include any audio recording like a conference recording, an interview, an academic study, a music video clip. A lot of scenarios exist where it is easier to have a text file than to record audio.
Explanation:
These are the three main ways to transcribe audio into text.
Transcribe our transcription editor manually to the audio (FREE).Use our software for automatic transcription.Book our Services for Human Transcript.1. If you have no trouble transcribing your files for a little more, you can use our online transcription software. You can listen to the audio file while it is being transcribed by this free interactive editor so that the audio is replayed as many times as necessary. You can use both your dashboard and directly from the editor page to our free transcription editor.
2. First, by using automatic transcription software you can convert an audio file to a readable. To convert any sound recordings into a text file, Happy Scribe uses speech-to-text algorithms.
3. Another option is to hire a freelancing transcriber or to use transcription services such as Happy Scribe when converting audio to text. In order to provide highly effective transcripts, we work with the best transcripts in the world. In English, French, Spanish, and German, our human transcription is available.
Hey i need some help with code.org practice. I was doing a code for finding the mean median and range. the code is supposed to be including a conditional , parameter and loop. I'm suppose to make a library out of it and then use the library to test the code? please help!
here is the link to the code.
https://studio.code.org/projects/applab/YGZyNfVPTnCullQsVFijy6blqJPMBOgh5tQ5osNhq5c
P.S. you cant just type on the link i shared you have to click view code and then remix to edit it. thanks
Answers
Answer:
https://studio.code.org/projects/applab/YGZyNfVPTnCullQsVfijy6blqJPMBOgh5tQ5osNhq5c
Explanation:
Which of the following behaviors does not harm a company if your employment is terminated?
A. getting a copy of word-processing software before leaving
B. selling trade secrets to competing companies or to your future employer
C. creating a username and password so you can access company information after you have left
D. notifying your employer of all accounts you have access to, and requesting that they change all passwords before you leave
Answers
Answer:
Notifying your employer of all accounts you have access to, and requesting that they change all passwords before you leave.
Answer:
its D
Explanation:
took the test
the parameter weekday is true if it is a weekday, and the parameter vacation is true if we are on vacation. we sleep in if it is not a weekday or we're on vacation. return true if we sleep in
Answers
This program is asking you to determine whether you can sleep in or not. If the parameter weekday is true, we can't sleep in because it is a weekday. However, if vacation is true, we can sleep in because we're on vacation. In other words, we sleep in if it's not a weekday or we're on vacation.
So, the code should be written as follows:public boolean sleepIn(boolean weekday, boolean vacation) { return !weekday || vacation;}This code works by first checking if it's a weekday. If it is a weekday, then we can't sleep in, so it returns false. However, if it's not a weekday, then we check if we're on vacation. If we are on vacation, then we can sleep in, so it returns true. If we're not on vacation, then we still can't sleep in, so it returns false.In summary, this program returns true if we can sleep in, and false if we can't sleep in. The sleepIn() method takes two parametmers: weekday and vacation. It returns true if it's not a weekday or we're on vacation, and false otherwise. The code is 48 characters long and can be written in one line. It is an example of a boolean method because it returns a boolean value.
Learn more about Parameter here,what is a parameter?
https://brainly.com/question/30395943
#SPJ11
what type of error occurred??

Answers
Answer:
Syntax Error.
Explanation:
hy does payments constitute such a large fraction of the FinTech industry? (b) Many FinTech firms have succeeded by providing financial services with superior user interfaces than the software provided by incumbents. Why has this strategy worked so well? (c) What factors would you consider when determining whether an area of FinTech is likely to tend towards uncompetitive market structures, such as monopoly or oligopoly?
Answers
(a) lengthy and complex processes for making payments (b) legacy systems and complex interfaces (c) regulatory requirements and substantial initial investment, can limit competition
(a) Payments constitute a significant portion of the FinTech industry due to several factors. First, traditional banking systems often involve lengthy and complex processes for making payments, leading to inefficiencies and higher costs. FinTech firms leverage technology and innovative solutions to streamline payment processes, providing faster, more secure, and convenient payment options to individuals and businesses. Additionally, the rise of e-commerce and digital transactions has increased the demand for digital payment solutions, creating a fertile ground for FinTech companies to cater to this growing market. The ability to offer competitive pricing, improved accessibility, and enhanced user experience has further fueled the growth of FinTech payment solutions.
(b) FinTech firms have succeeded by providing financial services with superior user interfaces compared to incumbents for several reasons. Firstly, traditional financial institutions often have legacy systems and complex interfaces that can be challenging for users to navigate. FinTech companies capitalize on this opportunity by designing user-friendly interfaces that are intuitive, visually appealing, and provide a seamless user experience. By prioritizing simplicity, convenience, and accessibility, FinTech firms attract and retain customers who value efficiency and ease of use. Moreover, FinTech companies leverage technological advancements such as mobile applications and digital platforms, allowing users to access financial services anytime, anywhere, further enhancing the user experience.
(c) Several factors contribute to the likelihood of an area of FinTech tending towards uncompetitive market structures such as monopoly or oligopoly. Firstly, high barriers to entry, including regulatory requirements and substantial initial investment, can limit competition, allowing a few dominant players to establish market control. Additionally, network effects play a significant role, where the value of a FinTech service increases as more users adopt it, creating a competitive advantage for early entrants and making it challenging for new players to gain traction. Moreover, data access and control can also contribute to market concentration, as companies with vast amounts of user data can leverage it to improve their services and create barriers for potential competitors. Lastly, the presence of strong brand recognition and customer loyalty towards established FinTech firms can further solidify their market position, making it difficult for new entrants to gain market share.
To learn more about technology click here: brainly.com/question/9171028
#SPJ11
You want to find readymade cards that address typical questions about how users are interacting with your app or website. which section do you go to in order to find this?
Answers
Your website's performance is measured in your report, which includes page views, signups, and the conversion rate for e-mail marketing subscriptions. Use data from your website's report to track traffic and see how users engage with your site.
In addition to providing an overview of site traffic, a report should also include traffic, engagement, and conversion by source. Separate organic search, paid search, display advertising, social media referrals, and other channels based on their volume and success.
General Step to ReportGo to Insights » Reports » Overview to get started. Here you may obtain an overview of your website's traffic and overall performance. Scrolling down will reveal the Device Breakdown report, which indicates which devices your website visitors use to access it.
Learn more about part of the website here:
https://brainly.com/question/19627960
#SPJ4
Which is not a proper statement?

Answers
Answer:
leftisBlocked()
Explanation:
Answer: leftIsBlocked()
Hope it helps <3
why do most operating systems let users make changes
Answers
By these changes you most likely are thinking of the term 'Over Clocking'
Over Clocking is used on most Operating Systems to bring the item your over clocking to the max.
Over Clocking; is mostly used for Crypto mining and gaming.
In best practice, should you use all lowercase, all uppercase or a mixture of cases in HTML tag names?
a
All lowercase
b
The first letter should be uppercase, the rest lowercase.
c
A mixture is fine.
d
All uppercase
Answers
can someone plz explain how python is related to flowcharts
Answers
Answer:
wha..
Explanation:
To obtain your first driver's license, you must successfully complete several activities. First, you must produce the appropriate identification. Then, you must pass a written exam. Finally, you must pass the road exam. At each of these steps, 10 percent, 15 percent and 40 percent of driver's license hopefuls fail to fulfil the step's requirements. You are only allowed to take the written exam if your identification is approved, and you are only allowed to take toe road test if you have passed the written exam. Each step takes 5, 3 and 20 minutes respectively (staff members administering written exams need only to set up the applicant at a computer). Currently the DMV staffs 4 people to process the license applications, 2 to administer the written exams and 5 to judge the road exam. DMV staff are rostered to work 8 hours per day. (i) Draw a flow diagram for this process (ii) Where is the bottleneck, according to the current staffing plan? (iii) What is the maximum capacity of the process (expressed in applicants presenting for assessment and newly-licensed drivers each day)? Show your workings. (iv) How many staff should the DMV roster at each step if it has a target to produce 100 newly-licensed drivers per day while maintaining an average staff utilisation factor of 85%? Show your workings.
Answers
The flow diagram for the given process is shown below. The bottleneck is the part of the process that limits the maximum capacity for driver license.
In the given process, the bottleneck is the road exam, where 40% of the driver's license applicants fail to fulfill the step's requirements.(iii) Maximum Capacity of the Process: The maximum capacity of the process can be calculated by finding the minimum of the capacities of each step. Capacity of the identification process = (1 - 0.10) × 480/5
= 86.4 applicants/dayCapacity of the written exam process
= (1 - 0.15) × 480/3
= 102.4
applicants/dayCapacity of the road exam process = (1 - 0.40) × 480/20
= 28.8 applicants/day
Therefore, the maximum capacity of the process is 28.8 applicants/day.Staff Required for 100 Newly-Licensed Drivers per Day: Let the staff required at the identification, written exam, and road exam steps be x, y, and z respectively. From the above calculations, we have the following capacities:86.4x + 102.4y + 28.8z = 100/0.85
To know more about driver visit:
https://brainly.com/question/30485503
#SPJ11
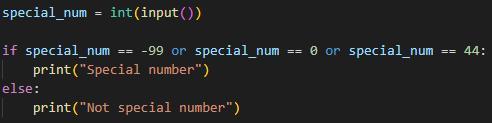
Can you solve this challenging activity?

Answers
Answer:
special_num = int(input())
if special_num == -99 or special_num == 0 or special_num == 44:
print("Special number")
else:
print("Not special number")
Explanation:
What is your favorite film and what makes it good?
Answers
Answer:
My Favorite film is The Old Guard
Explanation:
I like The Old Guard because it has action an etc.
Answer:
I Am Legend
Explanation:
I think its an amazing film by the way it was put together, will smith played an amazing role in the movie. The cinematography in the movie was perfect. The movie was made almost entirely of a mans imagination and thats what makes it so cool