Drag the tiles to the correct boxes to complete the pairs.
Match each type of database to its application
Multistage
Stationary
Distributed
Virtual
used for concise as well as detailed
historical data
arrowRight
used where access to data is rare
arrowRight
used for accessing data in diverse
applications using middleware
arrowRight
used by an organization that runs
several businesses
arrowRight
Answers
Answer:
1. Multistage database.
2. Stationary database.
3. Virtual database.
4. Distributed database.
Explanation:
A database management system (DBMS) can be defined as a collection of software applications that typically enables computer users to create, store, modify, retrieve and manage data or informations in a database. Generally, it allows computer users to efficiently retrieve and manage their data with an appropriate level of security.
There are four (4) major types of database in a data warehouse and these are;
1. Multistage database: used for concise as well as detailed historical data. It provides summarized data which can be used by an employee for short-term decision making.
2. Stationary database: used where access to data is rare i.e business firms who do not access data frequently. In order to use this database, the users must have an access to metadata store and thus, directly having access to the data on a source system.
3. Virtual database: used for accessing data in diverse applications using middleware. This type of database is dependent on having access to information on various databases.
4. Distributed database: used by an organization that runs several businesses. Therefore, this type of database are usually located or situated in various geographical regions.
Related Questions
Fill in the blank: While cleaning data, documentation is used to track _____. Select all that apply.
-errors
-deletions
-changes
-bias
Answers
While cleaning data, documentation is used to track errors, deletions, and changes. Hence option A is correct.
What is the documentation about?When cleaning data, it is important to maintain accurate and complete documentation in order to track the changes made to the data set. This includes documenting any errors that are identified and corrected, deletions of any data that is deemed irrelevant or inaccurate, and any changes made to the data such as formatting or coding adjustments.
Therefore, This documentation helps to ensure the integrity and accuracy of the data, and allows others to understand the cleaning process and any decisions that were made. It also helps to track the source of the errors, and to maintain a record of the original data for comparison, which is useful for auditing, version control, and reproducibility.
Learn more about documentation from
https://brainly.com/question/1218796
#SPJ1
In the file MajorSalary, data have been collected from 111 College of Business graduates on their monthly starting salaries. The graduates include students majoring in management, finance, accounting, information systems, and marketing. Create a PivotTable in Excel to display the number of graduates in each major and the average monthly starting salary for students in each major.
Answers
Answer:
The pivot table is attached below
Explanation:
procedure used to create the Pivot Table
select insert from worksheet Ribbonselect pivot tableselect the range of Dataselect "new worksheet "select Major as row heading and the summation symbol to count the majorinput variables given in their right cellsafter this procedure the table is successfully created
Attached below is the Pivot Table in Excel displaying The number of graduates in each major and average monthly salaries

Use the drop-down menu to complete the sentences about pseudocode.
Pseudocode provides a
Pseudocode
of what is happening in the computer program.
detail(s) every single step of the program.

Answers
Pseudocode provides a high-level overview of what is happening in a computer program
How does pseudocode do this?Pseudocode presents a broad perspective of the operations performed within a program by a computer. Acting as an intermediate phase bridging human-understandable language and executable code.
Although not outlining each step in a comprehensive manner, pseudocode captures the key steps and algorithms that are crucial in accomplishing the requested functionality.
The emphasis is on the coherence of the sequence of steps, the methods for making choices, and the significant functions, empowering developers to skillfully design and articulate the framework of their program well in advance of actual implementation in a given coding language.
Read more about pseudocode here:
https://brainly.com/question/24953880
#SPJ1
1 There are several applications to assist you to surf through the internet, mention
three (3 marks)
Answers
Web browsing
Peer-to-peer services
Help me with this with the question in the image

Answers
Answer:
1. I see value and form in there, and I see unity in there.
2. It create a better image by using words it also could inform people.
3. Maybe the you could add some cold color in it not just warm color.
You would like the cell reference in a formula to remain the same when you copy
it from cell A9 to cell B9. This is called a/an _______ cell reference.
a) absolute
b) active
c) mixed
d) relative
Answers
Answer:
The answer is:
A) Absolute cell reference
Explanation:
An absolute cell reference is used in Excel when you want to keep a specific cell reference constant in a formula, regardless of where the formula is copied. Absolute cell references in a formula are identified by the dollar sign ($) before the column letter and row number.
Hope this helped you!! Have a good day/night!!
Answer:
A is the right option absolutewhat number am i. i am less than 10 i am not a multiple of 2 i am a coposite
Answers
Answer: 9 is less than 10, it is odd (not a multiple of 2), and it is composite (since it has factors other than 1 and itself, namely 3). Therefore, the answer is 9.
design the logic for a program that allows a user to enter a number. display the sum of every number from 1 through the entered number
Answers
Answer: int sum = 1, n;
do {cin>>n; sum+=n;}while (n!=0);
cout<<sum;
Explanation:
is it true that if the user log out the computer will turn off automatically
Answers
Answer:
Yes it is true
Explanation:
7. A puzzle game featuring falling bricks which need to be3 organized on the screen describes which of the following very popular games from the 80s?
a) Tricks
b) Tetris
c) Sonics
d) Bricks
Answers
Answer:
Tetris
Explanation:
a really excellent way of getting you started on setting up a workbook to perform a useful function.
Answers
Templates a really excellent way of getting you started on setting up a workbook to perform a useful function.
What is the workbook about?One excellent way to get started on setting up a workbook to perform a useful function is to begin by defining the problem you are trying to solve or the goal you want to achieve. This will help you determine the necessary inputs, outputs, and calculations required to accomplish your objective.
Once you have a clear understanding of your goal, you can start designing your workbook by creating a plan and organizing your data into logical categories.
Next, you can start building the necessary formulas and functions to perform the required calculations and operations. This might involve using built-in functions such as SUM, AVERAGE, or IF, or creating custom formulas to perform more complex calculations.
Read more about workbook here:
https://brainly.com/question/27960083
#SPJ1
List and briefly describe various types of Malware?
Answers
Answer:
Here yah go.
Explanation:
Virus: A virus is a malicious program that attaches itself to legitimate files and spreads by infecting other files. It can cause damage to the infected system by corrupting or deleting files, slowing down the computer, or spreading to other connected devices.
Worm: Worms are self-replicating programs that spread over computer networks without the need for user interaction. They exploit vulnerabilities in operating systems or software to propagate themselves and can cause significant damage by consuming network bandwidth or carrying out malicious activities.
Trojan Horse: A Trojan horse appears as a legitimate and harmless program, but it contains malicious code that performs unauthorized activities without the user's knowledge. Trojans can enable remote access to a computer, steal sensitive information, or download and install additional malware.
Ransomware: Ransomware is a type of malware that encrypts a victim's files, making them inaccessible until a ransom is paid. It typically displays a ransom note, demanding payment in exchange for the decryption key. Ransomware attacks can be highly disruptive and costly for individuals and organizations.
Spyware: Spyware is designed to secretly monitor a user's activities and gather information without their consent. It can track keystrokes, capture screenshots, record browsing habits, and steal personal or sensitive data. Spyware often aims to collect financial information or login credentials.
Adware: Adware is a type of malware that displays unwanted advertisements on a user's computer. It can redirect web browsers, modify search results, and slow down system performance. Adware is typically bundled with legitimate software and generates revenue for its creators through advertising clicks or impressions.
Keylogger: Keyloggers are designed to record keystrokes on a computer or mobile device. They can capture usernames, passwords, credit card details, and other confidential information. Keyloggers can be delivered through malicious downloads, infected websites, or email attachments.
Botnet: A botnet is a network of compromised computers, also known as "zombies" or "bots," that are controlled by a central command and control (C&C) server. Botnets can be used for various malicious activities, including distributed denial-of-service (DDoS) attacks, spam distribution, or spreading other types of malware.
Rootkit: A rootkit is a type of malware that provides unauthorized access and control over a computer system while hiding its presence from detection by security software. Rootkits often modify operating system components and can be difficult to detect and remove.
Backdoor: A backdoor is a hidden entry point in a system that bypasses normal authentication mechanisms, allowing unauthorized access to a computer or network. Backdoors are often used by attackers to gain persistent access for further exploitation or to create a secret pathway for future access.
It is essential to stay vigilant, use reputable antivirus software, keep systems up to date, and exercise caution when downloading files or clicking on suspicious links to protect against these various types of malware.
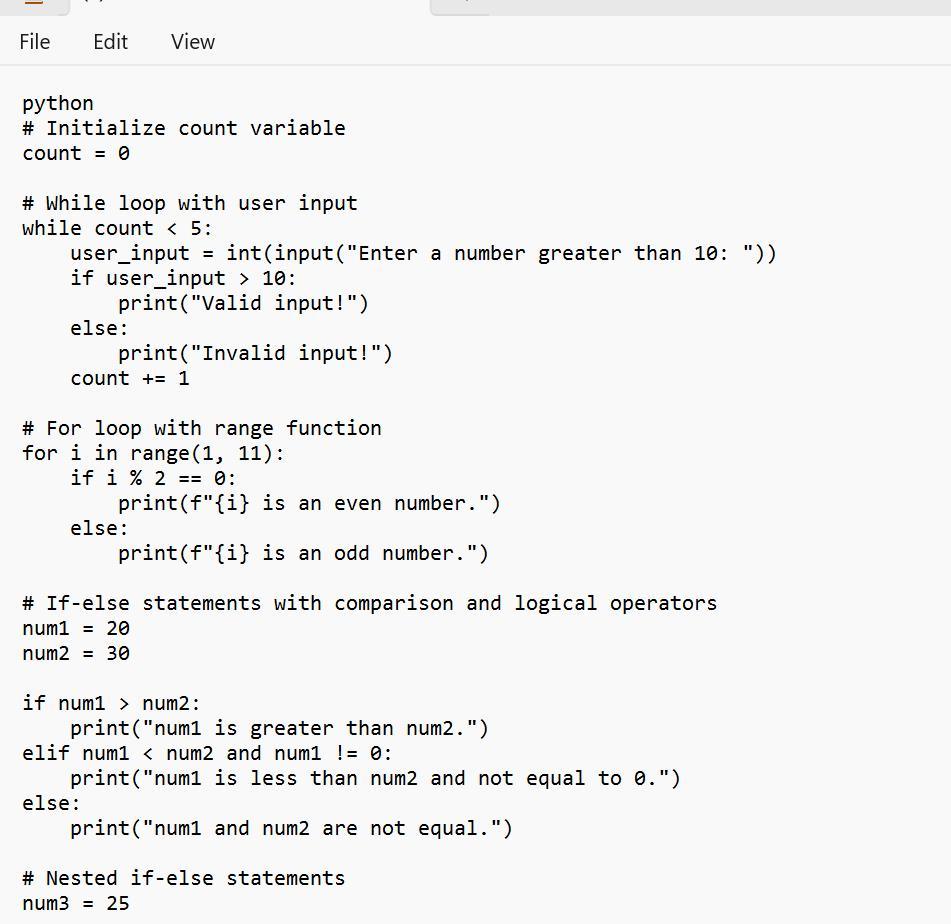
if-else AND if-elif-else
need at minimum two sets of if, one must contain elif
comparison operators
>, <, >=, <=, !=, ==
used at least three times
logical operator
and, or, not
used at least once
while loop AND for loop
both a while loop and a for loop must be used
while loop
based on user input
be sure to include / update your loop control variable
must include a count variable that counts how many times the while loop runs
for loop must include one version of the range function
range(x), range(x,y), or range(x,y,z)
comments
# this line describes the following code
comments are essential, make sure they are useful and informative (I do read them)
at least 40 lines of code
this includes appropriate whitespace and comments
python
Answers
Based on the image, one can see an example of Python code that is said to be able to meets the requirements that are given in the question:
What is the python?The code given is seen as a form of a Python script that tells more on the use of if-else as well as if-elif-else statements, also the use of comparison operators, logical operators, and others
Therefore, one need to know that the code is just a form of an example and it can or cannot not have a special functional purpose. It is one that is meant to tell more on the use of if-else, if-elif-else statements, etc.
Learn more about python from
https://brainly.com/question/26497128
#SPJ1

In JAVA with comments: Consider an array of integers. Write the pseudocode for either the selection sort, insertion sort, or bubble sort algorithm. Include loop invariants in your pseudocode.
Answers
Here's a Java pseudocode implementation of the selection sort algorithm with comments and loop invariants:
```java
// Selection Sort Algorithm
public void selectionSort(int[] arr) {
int n = arr.length;
for (int i = 0; i < n - 1; i++) {
int minIndex = i;
// Loop invariant: arr[minIndex] is the minimum element in arr[i..n-1]
for (int j = i + 1; j < n; j++) {
if (arr[j] < arr[minIndex]) {
minIndex = j;
}
}
// Swap the minimum element with the first element
int temp = arr[minIndex];
arr[minIndex] = arr[i];
arr[i] = temp;
}
}
```The selection sort algorithm repeatedly selects the minimum element from the unsorted part of the array and swaps it with the first element of the unsorted part.
The outer loop (line 6) iterates from the first element to the second-to-last element, while the inner loop (line 9) searches for the minimum element.
The loop invariant in line 10 states that `arr[minIndex]` is always the minimum element in the unsorted part of the array. After each iteration of the outer loop, the invariant is maintained.
The swap operation in lines 14-16 exchanges the minimum element with the first element of the unsorted part, effectively expanding the sorted portion of the array.
This process continues until the entire array is sorted.
Remember, this pseudocode can be directly translated into Java code, replacing the comments with the appropriate syntax.
For more such questions on pseudocode,click on
https://brainly.com/question/24953880
#SPJ8
true or false. Two of the main differences between storage and memory is that storage is usually very expensive, but very fast to access.
Answers
Answer:
False. in fact, the two main differences would have to be that memory is violate, meaning that data is lost when the power is turned off and also memory is faster to access than storage.
Drag each tile to the correct box.
Match the job title to its primary function.
computer system engineer
online help desk technician
document management specialist
design and implement systems for data storage
data scientist
analyze unstructured, complex information to find patterns
implement solutions for high-level technology issues
provide remote support to users
Answers
The correct match for each job title to its primary function:
Computer System Engineer: Design and implement systems for data storage.
Online Help Desk Technician: Provide remote support to users.
Document Management Specialist: Implement solutions for high-level technology issues.
Data Scientist: Analyze unstructured, complex information to find patterns.
Who is a System Engineer?The key responsibility of a computer system engineer is to develop and execute data storage systems. Their main concentration is on developing dependable and effective storage options that fulfill the company's requirements.
The primary duty of an online help desk specialist is to offer remote assistance to users, addressing their technical concerns and resolving troubleshooting queries.
The main responsibility of a specialist in document management is to introduce effective measures to address intricate technological matters pertaining to document security, organization, and retrieval.
Read more about data scientists here:
https://brainly.com/question/13104055
#SPJ1
The differences between client based projects and community based projects in terms of staging and live server
Answers
The differences between client based projects and community based projects in terms of staging and live server is that Client Server Based Live Meeting project system is one where the users are said to be making use of third party public mail services while the other does not.
What purpose does a live server serve?The working directory as well as its subdirectories are served by the server, a straightforward node app. It also keeps an eye on the files for changes, and when one occurs, it notifies the browser to reload by sending a message over a web socket connection.
Therefore, Before graduating, client-based projects (CBPs) give students abundant possibilities for hands-on learning and the chance to put their knowledge to use by meeting the demands of actual clients.
Learn more about client based projects from
https://brainly.com/question/28102768
#SPJ1
How can you compute, the depth value Z(x,y) in
z-buffer algorithm. Using incremental calculations
find out the depth value Z(x+1, y) and Z (x, y+1).
(2)
Answers
The Depth-buffer approach, usually referred to as Z-buffer, is one of the methods frequently used to find buried surfaces. It is a method in image space and pixel.
Thus, The pixel to be drawn in 2D is the foundation of image space approaches and Z buffer. The running time complexity for these approaches equals the product of the number of objects and pixels.
Additionally, because two arrays of pixels are needed—one for the frame buffer and the other for the depth buffer—the space complexity is twice the amount of pixels.
Surface depths are compared using the Z-buffer approach at each pixel location on the projection plane.
Thus, The Depth-buffer approach, usually referred to as Z-buffer, is one of the methods frequently used to find buried surfaces. It is a method in image space and pixel.
Learn more about Z buffer, refer to the link:
https://brainly.com/question/12972628
#SPJ1
A program is required to compute the cost of a car trip. The required input values are:
Litres per 100km
Distance travelled
Cost per litre of petrol
The output value is the total cost of the trip.
Answers
The program required to compute the above in Phyton is given below.
What is the program that computes the cost of a car trip using the above parameters?the required program is given as follows;
# Input values
litres_per_100km = float(input("Enter the fuel efficiency of your car in litres per 100km: "))
distance_travelled = float(input("Enter the distance travelled in km: "))
cost_per_litre = float(input("Enter the cost per litre of petrol in your local currency: "))
# Calculate the total litres of petrol used
litres_used = (litres_per_100km / 100) * distance_travelled
# Calculate the total cost of the trip
total_cost = litres_used * cost_per_litre
# Display the result
print(f"The total cost of the trip is {total_cost:.2f} {currency_symbol}")
Note that this program prompts the user to enter the fuel efficiency of their car in litres per 100km, the distance travelled in km, and the cost per litre of petrol in their local currency.
It then calculates the total litres of petrol used by multiplying the fuel efficiency by the distance travelled, and calculates the total cost of the trip by multiplying the litres used by the cost per litre.
Finally, it displays the result to the user, rounded to two decimal places. Note that the currency symbol can be added to the output string depending on the user's location.
Learn more about phyton:
https://brainly.com/question/16757242
#SPJ1
How could you use a spreadsheet you didn't like to simplify access also the problem
Answers
Explanation:
......
Which of the following accurately describes a user persona? Select one.
Question 6 options:
A user persona is a story which explains how the user accomplishes a task when using a product.
A user persona should be based only on real research, not on the designer’s assumptions.
A user persona should include a lot of personal information and humor.
A user persona is a representation of a particular audience segment for a product or a service that you are designing.
Answers
A user persona is a fictionalized version of your ideal or present consumer. In order to boost your product marketing, personas can be formed by speaking with people and segmenting them according to various demographic and psychographic data and user.
Thus, User personas are very helpful in helping a business expand and improve because they reveal the various ways customers look for, purchase, and utilize products.
This allows you to concentrate your efforts on making the user experience better for actual customers and use cases.
Smallpdf made very broad assumptions about its users, and there were no obvious connections between a person's occupation and the features they were utilizing.
The team began a study initiative to determine their primary user demographics and their aims, even though they did not consider this to be "creating personas," which ultimately helped them better understand their users and improve their solutions.
Thus, A user persona is a fictionalized version of your ideal or present consumer. In order to boost your product marketing, personas can be formed by speaking with people and segmenting them according to various demographic and psychographic data and user.
Learn more about User persona, refer to the link:
https://brainly.com/question/28236904
#SPJ1
Write a program that receives a series of numbers from the user and allows the user to press the enter key to indicate that he or she is finished providing inputs. After the user presses the enter key, the program should print the sum of the numbers and their average.
Answers
The program that receives a series of numbers from the user is:
theSum = 0.0
# stores the number of terms entered by the user
n = 0
# loop until user presses the enter key
# infinite loop
while True:
# get user input from user
data = input("Enter a number or press Enter to quit: ")
# if user presses enter
if data == '':
# break out of the loop
break
# convert data into float using float()
number = float(data)
# add the entered number to theSum
theSum += number
# increase the number of terms
n += 1
print()
print("The sum is", theSum)
# if numbers of terms entered are greater than 0
if n > 0:
# calculate average
average = theSum / n
print('The average is', average)
# if no terms are entered
else:
print('Average : undefined (as the number of terms entered are 0)')
What is a program?A computer program is a set of instructions written in a programming language that a computer is supposed to obey.
Computer programs are one of the intangible components of the software, which also includes documentation and other components. The version of a computer program that humans can read is called the source code.
Learn more about program on;
https://brainly.com/question/23275071
#SPJ1

Discuss the Von-Neumann CPU architecture?
Answers
The Von Neumann architecture is a traditional CPU design named after John von Neumann and widely implemented since the mid-20th century.
What is the Von-Neumann CPU architecture?Basis for modern computers, including PCs, servers, and smartphones. Von Neumann architecture includes components for executing instructions and processing data. CPU is the core of Von Neumann architecture.
It manages operations, execution, and data flow in the system. Von Neumann architecture stores both program instructions and data in a single memory unit. Memory is organized linearly with each location having a unique address. Instructions and data are stored and retrieved from memory while a program runs.
Learn more about Von-Neumann CPU architecture from
https://brainly.com/question/29590835
#SPJ1
Describe what the 4th I.R. Means; and List the 4 most Important Variables of the How the 4th I.R. will change the lives of how we would Live and Work?
Answers
Answer:
The Fourth Industrial Revolution (4IR) is the ongoing transformation of the traditional manufacturing and industrial sectors through the integration of advanced technologies such as artificial intelligence, the Internet of Things (IoT), robotics, big data, and automation.
The four most important variables that will change the way we live and work in the 4IR are:
Automation: The increased use of robotics and automation will revolutionize the manufacturing industry and lead to more efficient and cost-effective production processes. This could lead to significant job displacement, but it could also create new opportunities for workers with new skills.
Big Data: The collection and analysis of massive amounts of data will allow businesses to gain new insights into customer behavior, supply chain efficiency, and product performance. This could lead to more personalized and efficient services, but also raise concerns around privacy and data security.
Artificial Intelligence: The use of advanced algorithms and machine learning will enable machines to perform complex tasks previously thought to require human intelligence. This could lead to more efficient and effective decision-making, but also raise concerns around the impact on jobs and the ethical implications of AI decision-making.
Internet of Things: The proliferation of connected devices will enable the automation and integration of various systems and processes, leading to more efficient and effective resource utilization. This could lead to significant improvements in healthcare, transportation, and energy management, but also raise concerns around privacy and security risks.
Overall, the 4IR is expected to bring significant changes to our economy, society, and daily lives, with both opportunities and challenges that we will need to navigate as we move forward.
A mysql prompt has been opened for you. Using the college database, complete the following tasks (use either a single-line or a multi-line SQL statement): Create a courses table with this definition (try using a multi-line SQL statement): --------- --------------------- ------ ----- --------- ---------------- | Field | Type | Null | Key | Default | Extra | --------- --------------------- ------ ----- --------- ---------------- | id | int(3) unsigned | NO | PRI | NULL | auto_increment | | title | varchar(255) | NO | UNI | NULL | | | credits | tinyint(2) unsigned | NO | | 1 | | --------- --------------------- ------ ----- --------- ---------------- Once you have completed these tasks press the Check It! button to have your solution assessed.
Answers
Answer:
See Explanation
Explanation:
Given
See attachment 1 for proper table definition
To answer this question, one of the basic sql commands (the "create" command) will be used to create the required table, followed by the fields of the table.
I could not submit my answer directly. So, I added two additional attachments which represent the answer section and the explanation section, respectively.



Which orientation style has more height than width?
Answers
Answer:
"Portrait orientation" would be the correct answer.
Explanation:
The vertical picture, communication as well as gadget architecture would be considered as Portrait orientation. A webpage featuring portrait orientation seems to be usually larger than large containing lettering, memo abases as well as numerous types of content publications.One such volume fraction also becomes perfect for impressionism depicting an individual from either the top.Thus the above is the correct answer.
In HTML5, the
(line break) tag does not require a closing tag.
true or false
Answers
The ___ bar changes depending on which tool is currently selected…?
Answers
Answer: Options (I'm not 100% sure but I think its options.) Have a nice day!
Answer:
Options (I'm not 100% sure but I think it's options.) Have a nice day!
Explanation:
Name two looping mechanisms used in Perl.
Answers
what is the symbol for population mean
Answers
The symbol for population mean is μ (mu).
The symbol μ (mu) is used to represent the population mean in statistics. The population mean is a measure of central tendency that represents the average value of a variable in the entire population.
It is calculated by summing up all the values in the population and dividing by the total number of observations.
The use of the Greek letter μ as the symbol for population mean is a convention in statistics. It helps to distinguish the population mean from other measures of central tendency, such as the sample mean .
The population mean provides valuable information about the average value of a variable in the entire population, which can be useful for making inferences and drawing conclusions about the population as a whole.
The population mean is a useful statistic because it provides a single value that summarizes the central tendency of the variable in the population. It helps researchers and statisticians understand the typical or average value of the variable and make comparisons or draw inferences about the population as a whole.
It's important to note that the population mean is based on data from the entire population, which is often not feasible or practical to obtain in many cases. In such situations, researchers often rely on samples to estimate the population mean.
For more questions on population
https://brainly.com/question/30396931
#SPJ11